4.15
VeraCrypt - A cross platform, free, open source disk encryption software
An utility for on-the-fly encryption. The software can create a virtual encrypted disk that works just like a regular disk but within a file. It can also encrypt a partition or the entire storage device with pre-boot authentication.
Category: software, open source, free, encryption, security
Stable Version: VeraCrypt 1.25.9
Release Date: 2022-02-19
Runs on: windows, mac, linux, openbsd, freebsd





Download
VeraCrypt/ Install Binaries: Links on the Official Website
Disclaimer: We do not store any binary or executable file formats on this website to provide direct file downloads. All download links of binaries or executables presented on this website, for any software application without exception, are provided only from the application's publisher Official Website and no other locations. This website is not responsible for the accuracy or safety of the software applications presented here. In particular this website section is just a catalog with popular opensource software applications mainly addressed to software developers to easy the access to the open source code.
Get the Source Code of
VeraCrypt/ Software Source Code Download
Specifications:
- Project Developer:
IDRIX
- License: Apache License 2.0 and TrueCrypt License 3.0
- OpenSource, Free: Yes
- Written in:
C,C++,Assembly
Building from Source: dependencies
- WxWidgets
- Yasm, Sudo
- LLVM or GCC compiler
Review
0
5
4.8
w3soft.org
VeraCrypt adds enhanced security to the algorithms used for system and partitions encryption making it immune to new developments in brute-force attacks. It also solves many vulnerabilities and security issues found in TrueCrypt. As an example, when the system partition is encrypted, TrueCrypt uses PBKDF2-RIPEMD160 with 1000 iterations whereas this software uses 327661. And for standard containers and other partitions, TrueCrypt uses at most 2000 iterations but VeraCrypt uses 655331 for RIPEMD160 and 500000 iterations for SHA-2 and Whirlpool.
This enhanced security adds some delay only to the opening of encrypted partitions without any performance impact to the application use phase. This is acceptable to the legitimate owner but it makes it much harder for an attacker to gain access to the encrypted data. Starting from version 1.12, it is possible to use custom iterations through the PIM feature, which can be used to increase the encryption security. Starting from version 1.0f, it can load a TrueCrypt volume. It also offers the possibility to convert TrueCrypt containers and non-system partitions to VeraCrypt format.
Pros +
- the TrueCrypt license is generally considered to be source-available but not free and open source ; the Apache license is universally considered to be free and open source ; the mixed VeraCrypt license is widely considered to be free and open source
- cross platform, free, can be ported to almost any operating system
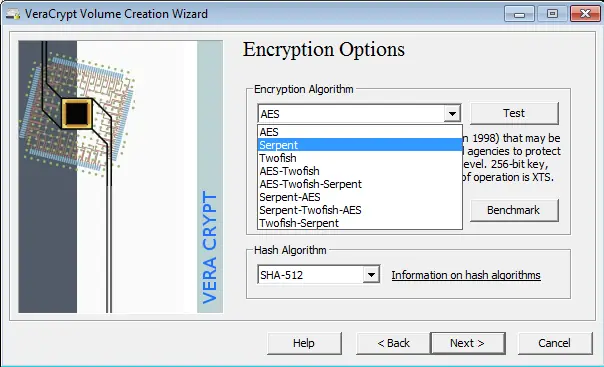
- it offers standard strong encryption by allowing a variety of crypto algorithms such as:
AES,Serpent,Twofish,Camellia, andKuznyechik; it also offers the possibility to cascade these algorithms in any combination - the cryptographic hash functions available for use are very strong such as
RIPEMD-160,SHA-256,SHA-512,StreebogandWhirlpool - it's block cipher mode of operation is XTS ; it generates the header key and the secondary header key (XTS mode) using
PBKDF2with a512-bitsalt - the software development team considered the TrueCrypt storage format too vulnerable to a National Security Agency (NSA) attack, so it created a new format incompatible with that of TrueCrypt thus VeraCrypt is still capable of opening and converting volumes in the TrueCrypt format
- it also supports parallelized encryption on multi-core systems which makes it really fast
Cons -
- There are several kinds of attacks to which all software-based disk encryption is vulnerable ; as with TrueCrypt, the VeraCrypt documentation instructs users to follow various security precautions to mitigate these attacks such as:
- Encryption keys stored in memory
- Tampered hardware
- Trusted Platform Module
About
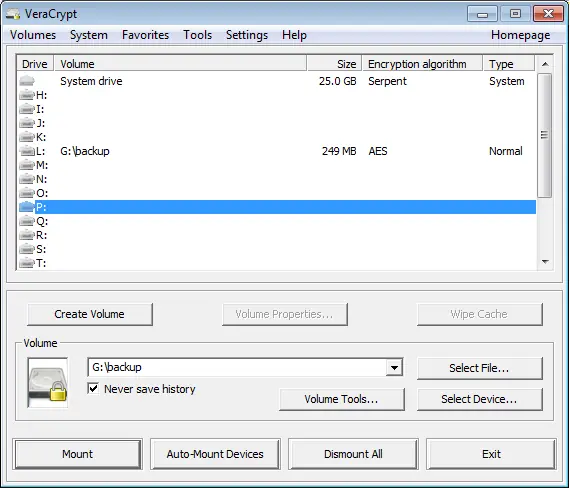
VeraCrypt is a software for establishing and maintaining an on-the-fly-encrypted volume (data storage device). On-the-fly encryption means that data is automatically encrypted right before it is saved and decrypted right after it is loaded, without any user intervention. No data stored on an encrypted volume can be read (decrypted) without using the correct password/keyfile(s) or correct encryption keys. Entire file system is encrypted (e.g., file names, folder names, contents of every file, free space, meta data, etc).
Features
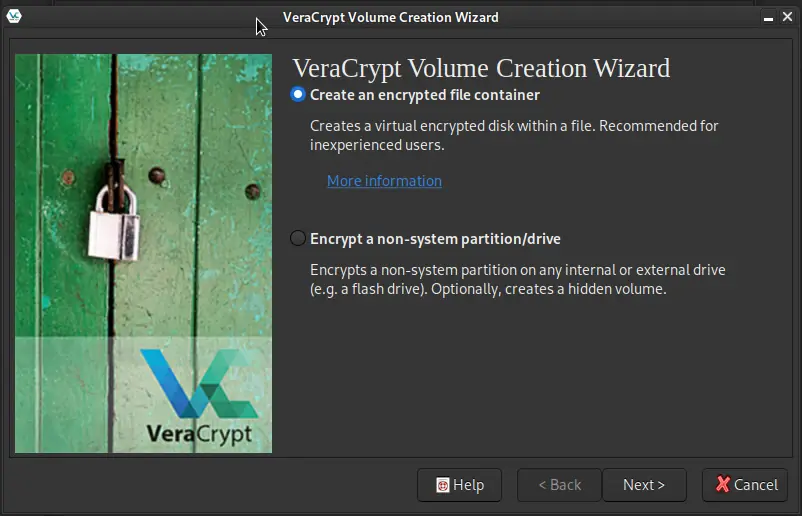
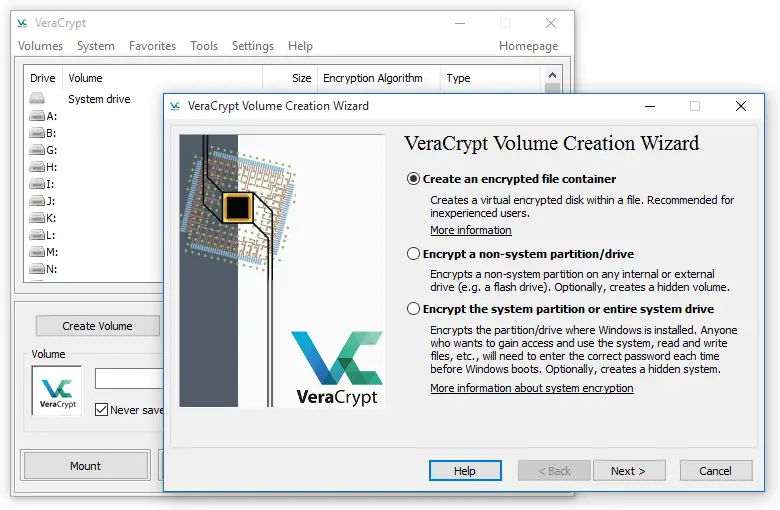
- Creates a virtual encrypted disk within a file and mounts it as a real disk.
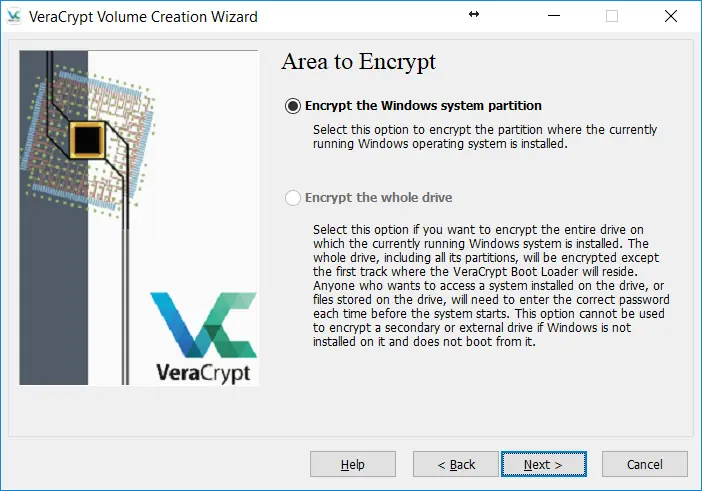
- Encrypts an entire partition or storage device such as USB flash drive or hard drive.
- Encrypts a partition or drive where Windows is installed (pre-boot authentication).
- Encryption is automatic, real-time(on-the-fly) and transparent.
- Parallelization and pipelining allow data to be read and written as fast as if the drive was not encrypted.
- Encryption can be hardware-accelerated on modern processors.
- Provides plausible deniability, in case an adversary forces you to reveal the password: Hidden volume (steganography) and hidden operating system.
- More information about the features of this software may be found in the documentation
Security Overview
Files can be copied to and from a mounted volume just like they are copied to/from any normal disk (for example, by simple drag-and-drop operations). Files are automatically being decrypted on the fly (in memory/RAM) while they are being read or copied from an encrypted volume. Similarly, files that are being written or copied to the volume are automatically being encrypted on the fly (right before they are written to the disk) in RAM. Note that this does not mean that the whole file that is to be encrypted/decrypted must be stored in RAM before it can be encrypted/decrypted. There are no extra memory (RAM) requirements for this application. For an illustration of how this is accomplished, see the following paragraph.
Note that it never saves any decrypted data to a disk - it only stores them temporarily in RAM (memory). Even when the volume is mounted, data stored in the volume is still encrypted. When you restart the operating system or turn off your computer, the volume will be dismounted and files stored in it will be inaccessible (and encrypted). Even when power supply is suddenly interrupted (without proper system shut down), files stored in the volume are inaccessible (and encrypted). To make them accessible again, you have to mount the volume (and provide the correct password and/or keyfile).
Plausible Deniability
In case an adversary forces you to reveal your password, it provides and supports two kinds of plausible deniability:
- Hidden volumes (volumes that are hidden from the operating systems)
- Until decrypted, a partition/device/file encrypted with this software appears to consist of nothing more than random data (it does not contain any kind of "signature") ; therefore, it should be impossible to prove that a partition or a device or a file is a VeraCrypt volume or that it has been encrypted
It can be used to securely erase a partition/device too, by creating an empty encrypted partition/device-hosted volume within it). However, you need to prevent data leaks (see the section Data Leaks) and also note that, for system encryption, the first drive track contains the (unencrypted) VeraCrypt Boot Loader, which can be easily identified as such.
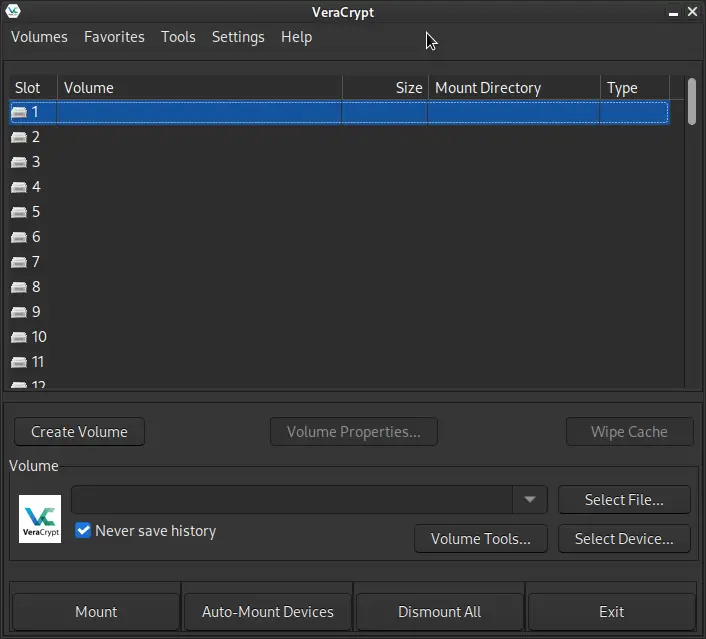
Screenshot: Main Screen
Changelog Highlights
2022-02-19 : version 1.25.9
notable changes
- Update translations
- Windows - Make MSI installer compatible with system encryption ; Set minimum support for MSI installation to Windows 7
- Fix failure to create Traveler Disk when VeraCrypt is installed using MSI
- Don't cache the outer volume password when mounting with hidden volume protection if wrong hidden volume password was specified
- Reduce the size of EXE installers by almost 50% by using LZMA compression instead of DEFLATE
- Fix double-clicking mounted drive in VeraCrypt UI not working in some special Windows configurations
- MacOS - Fix hidden volume settings not correctly displayed when enabling hidden volume protection in mount options window
- Linux - Fix hidden volume settings not correctly displayed when enabling hidden volume protection in mount options window
- Fix generic Linux installer overwriting /usr/sbin if it is a symlink
- Fix crash when building with _GLIBCXX_ASSERTIONS defined
- Enable building from source without AES-NI support
2022-01-07 : version 1.25.7
notable changes
- Restore support of Windows Vista, Windows 7 and Windows 8/8.1
- MSI installation only: Fix double-clicking .hc file container inserting %1 instead of volume name in path field
- Advanced users: Add registry settings to control driver internal encryption queue to allow tuning performance for SSD disks and having better stability under heavy load
- MacOS: Fix resource files inside VeraCrypt application bundle (e.g. HTML documentation, languages XML files) being world-writable
2021-12-03 : version 1.25.4
notable changes
- Speed optimization of Streebog
- Update translations
- Add support for Windows on ARM64
- Drop support of Windows Vista, Windows 7, Windows 8 and Windows 8.1 because of new requirement for driver code signing
- Reduce time of mount when PRF auto-detection is selected
- Fix potential memory corruption in driver caused by integer overflow in IOCTL_STORAGE_MANAGE_DATA_SET_ATTRIBUTES
- Replace insecure wcscpy/wcscat/strcpy runtime functions with secure equivalents
- Changes to EFI bootloader: Fix memory leak in some cases ; Clear bootParams variable that may contain sensitive information ; Add option "KeyboardInputDelay" in DcsProp to control the minimum delay supported between two key strokes
- Fix freeze when password dialog displayed in secure desktop and try to access token keyfiles protected by PIN
- Fix failure to launch keyfile generator in secure desktop mode
- Block Windows from resizing system partition if it is encrypted
- Add keyboard shortcut to "TrueCrypt mode" in the mount dialog
- MacOS: Native support of Apple Silicon M1
- Drop official support of Mac OS X 10.7 Lion and Mac OS X 10.8 Mountain Lion
- MacOS - Return error if unknown filesystem value specified in CLI --filesystem switch instead of silently skipping filesystem creation
- Linux: Compatiblity with with pam_tmpdir
- Add CLI switch (--size=max) and UI option to give a file container all available free space on the disk where it is created
- Return error if unknown filesystem value specified in CLI --filesystem switch instead of silently skipping filesystem creation
- OpenBSD: Add basic support
- FreeBSD: Make system devices work